We Deepfaked Bob (with his consent)
Deepfakes have been headline‑news for years, but 2025 marks the moment they crossed an important threshold: video deepfakes that need…
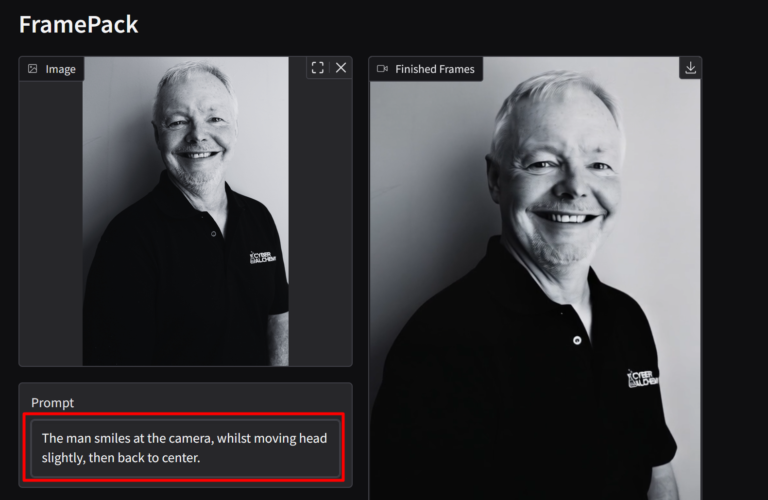
Deepfakes have been headline‑news for years, but 2025 marks the moment they crossed an important threshold: video deepfakes that need…
AI bias isn’t hypothetical it’s happening now. From subtle censorship to corporate influence, learn how LLMs are being shaped and why it matters.
AI is driving efficiency and innovation in business. But have you considered the security risks? Many business leaders, eager to…

Work has never been more flexible. Remote teams, cloud-based collaboration, and bring-your-own-device (BYOD) policies have made office-based work smoother and…

Injection attacks remain one of the biggest cyber threats. They take advantage of input fields and data-processing tools to break…

So, you’ve secured your own network, but what about the dozens of vendors you work with daily? Think about it. …
To access your exclusive guide today, fill in the form below.
To access your exclusive guide today, fill in the form below.