Abuse of Trusted Channels for Modular Infostealer and Malware Delivery
Cybercriminals are increasingly abusing trusted distribution channels, such as open-source platforms, online advertisements, search engines, package repositories, and cloud services, to deliver modular infostealer malware.
These tactics exploit the inherent trust in popular platforms (e.g. GitHub, advertising networks, Google search, package managers, and cloud storage) to slip malicious payloads past traditional defences.
Once executed, modern infostealers typically run in a multi-stage, modular fashion: an initial dropper establishes a foothold, then fetches additional modules to perform system reconnaissance, credential theft, data exfiltration, and persistence (Microsoft security research). In parallel, defenders deploy layered controls (from reputation filtering and sandbox detonation to behaviour-based detection, endpoint protection, browser isolation, and user education) to break these attack chains at multiple points.
This post examines recent attacker techniques (with emphasis on the past year) and evaluates how effective layered defences are in disrupting end-to-end attack chains.
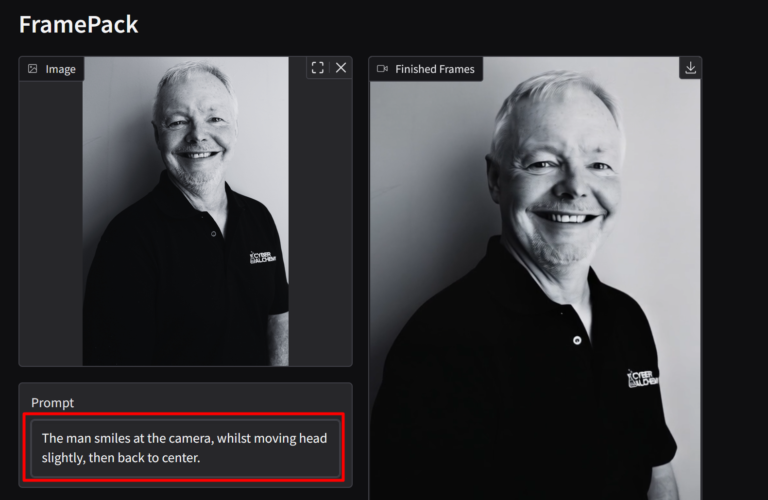
Note: We include a short demo of a live GitHub repository reached via a Google-sponsored link. The malware appears to have been removed, but exercise caution before interacting with any linked content.
TD;DR
- Bad actors abuse a trusted channel (e.g. a Google Ad).
- The ad links to a legitimate domain (e.g. github.com).
- The GitHub page mimics a legitimate repo but uses an orphaned fork.
- The fork contains malicious download links.
- Anchor text hides the true destination and presents a convincing download page.
- The user clicks through to a typosquatted site (e.g. git-hub-software[.]com).
- The software runs; if AV/EDR does not block quickly, it steals data (sessions, passwords, etc.) and pulls additional payloads.
Even if EDR intervenes, passwords/tokens may already be compromised, so reset credentials and revoke sessions.

Abusing Trusted Channels: Techniques and Trends (Last 12 Months)
Malicious GitHub Repositories and Forks
GitHub has become a significant malware distribution channel because developers trust it. Attackers create fake repositories, fork popular projects, and operate ghost accounts to spread malware.
In mid-2024, a threat group dubbed Stargazer Goblin reportedly operated a malware Distribution-as-a-Service model on GitHub, creating thousands of fake accounts to push info-stealers (part of a so-called “Stargazer’s Ghost Network. Malicious content (often password-protected ZIPs) is dressed up with stars, forks, and watchers to appear legitimate (BleepingComputer coverage). Delivered families included RedLine, Lumma, Rhadamanthys, RisePro, and Atlantida, often themed to attract cryptocurrency, gaming, or social media communities (see BleepingComputer).
Another tactic is the use of trojanized or cloned repositories. In early 2024, a “mirror poisoning” case occurred involving a fake Python package index that hosted a malicious package impersonating colorama. It was disseminated via a compromised community account and infecting a large number of users with an info-stealer payload (Forklog report). Around March 2024, researchers also noted a surge of over 100,000 malicious GitHub repositories aimed at developers: an at-scale attempt to infect users who pull code that appears legitimate (see Forklog). If malware such as this is executed, it can steal browser data, session tokens, cloud credentials, and cryptocurrency wallet keys.
Malvertising and SEO Poisoning Campaigns
Attackers are increasingly leveraging malvertising (malicious ads) and SEO poisoning (manipulating search engine rankings) to direct users to malware hosted on trusted websites.
Late 2024 saw a large-scale malvertising campaign that impacted nearly one million devices, where illegal streaming sites redirected users through pay-per-click chains to malware downloads hosted on GitHub, Discord CDN, and Dropbox (trusted domains that can evade simple reputation filters). The multi-stage chain started with a dropper from GitHub, followed by scripts and payloads that escalated to full infostealers or RATs.
In 2025, AI-themed SEO lures (masquerading as tools like “ChatGPT” or “Luma”) employed black-hat SEO tactics to achieve top search results. Visitors to these sites encountered JavaScript-driven redirects with browser fingerprinting, avoiding sandboxes and ultimately delivering Vidar, Lumma, or loaders like Legion (Zscaler ThreatLabz).
Payloads are often packaged as very large installers to evade time/size-constrained sandboxes. One mid-2024 campaign used typosquatting to impersonate software download sites and delivered a 600 MB fake installer containing an obfuscated Poseidon/AMOS infostealer targeting macOS (Hunt.io analysis).
Package Manager Typosquatting and Supply-Chain Attacks
Open-source package repositories such as PyPI (Python) and npm (Node.js) are frequent targets. In March 2024, PyPI halted new registrations for roughly ten hours to purge a flood of malicious, uploaded typosquats of popular library names.
Encrypted, malicious code was hidden in setup.py install scripts, so simply installing the package executed a loader that fetched a second-stage infostealer. Final payloads harvested browser credentials, crypto keys, and other sensitive data, and added persistence (Checkmarx research).
Cross-platform campaigns also emerged. In October 2024, Datadog Security Labs detailed a cluster (MUT-8694) that targeted both PyPI and npm, utilising packages that employed post-install hooks (PowerShell or JavaScript) to download Windows malware from GitHub and Replit. The cluster delivered commodity stealers like Blank Grabber and Skuld Stealer.
Over 40 malicious Python and 18 npm packages were linked to this operation, often disguised as Roblox/game APIs or system utilities (Datadog Security Labs).
A novel March 2024 “fake registry mirror” attack mimicked the real PyPI, tricking users into installing a trojanized version of colorama that executed a multi-stage infostealer targeting browser data and messaging tokens (see Forklog). The sophistication highlights how far adversaries will go to subvert trust in official ecosystems.
Cloud Storage and CDN Abuse
Adversaries are increasingly exploiting cloud storage and CDN services for both payload delivery and command-and-control (C2) purposes. CLOUD#REVERSER (mid-2024) used Google Drive and Dropbox as staging servers. A dropper (disguised as an Excel file via a Unicode trick) set scheduled tasks that periodically pulled scripts and binaries from attacker-controlled cloud folders, blending in with regular traffic to *.googleusercontent.com and dl.dropboxusercontent.com (The Hacker News). Because organisations commonly allow these domains, network-based blocks are less effective. Similar patterns appear across OneDrive, Amazon S3, Cloudflare Workers, and IPFS gateways (e.g. Cloudflare IPFS) to disguise malicious delivery (see The Hacker News).
Modular, Multi-Stage Infostealers: “Stealership” on the Rise
Contemporary infostealers (e.g. Lumma, Raccoon v2, Vidar, RedLine) often comprise small initial implants that fetch on-demand modules, keeping the first stage lightweight and less suspicious. Microsoft’s analysis of malvertising-to-GitHub chains describes a four-stage kill chain:
- GitHub dropper establishes a foothold (often with a signed binary);
- The second stage performs discovery and basic exfiltration.
- Adaptive third stage selects a loader/RAT or an infostealer (sometimes launched via LOLBins like MSBuild.exe, mshta.exe, or regsvr32);
- Final modules dump browser credentials, exfiltrate files, capture keystrokes, and beacon over encrypted channels (Microsoft security blog).
Defence evasion is standard: sandbox/virtualisation checks, EDR tampering, and security setting modifications (e.g., adding Defender exclusions). In the PyPI cases, the first stage simply retrieved an encrypted second stage from a URL constructed on the fly. Only then did the full infostealer activate (Checkmarx). The modular design enables targeted payloading (e.g. only deploy a wallet module if crypto artefacts are detected) and complicates analysis.
Effectiveness of Layered Defensive Controls
Reputation Systems and Allow-List Filtering
Domain/IP reputation, URL filtering, and file reputation (e.g. SmartScreen) remain a first line of defence. However, when attackers operate on reputable domains, such as GitHub, Discord CDN, Dropbox, and Google Drive, pure reputation approaches struggle. SEO poisoning often relies on new or compromised legitimate domains, including government and university sites, as seen in SolarMarker campaigns (Menlo Security). Reputation still helps once indicators are known, and application allow-listing can block untrusted binaries by age/prevalence. Treat it as necessary but insufficient (BleepingComputer, The Hacker News).
Sandboxing and Detonation
Detonation chambers and sandboxes catch many threats by observing runtime behaviour, but attackers increasingly evade them with oversized installers, multi-stage delays, user-interaction gates, and environment checks. Campaigns delivering 100 MB+ or 600 MB installers aim to exceed size/time limits and to avoid automated analysis (Menlo Security, Hunt.io, Zscaler). Sandboxing remains valuable, mainly when results feed EDR in near real-time, but it is just one layer in the stack.
Runtime Behaviour Analysis (EDR/XDR)
EDR/XDR tools detect post-execution patterns (credential store access, suspicious scheduled tasks, LOLBin abuse, process injection, and anomalous network beacons). Properly tuned solutions (ideally in block mode) can terminate unknown malware based on behaviour and isolate hosts automatically. Adversaries will still attempt EDR avoidance and process killing, so coverage and policy configuration are critical (Microsoft Defender for Endpoint).
Endpoint Protection (AV) and Content Scanning
Traditional AV struggles with fresh, packed, or fileless malware but benefits from cloud heuristics and rapid signature updates once samples are shared. Attack Surface Reduction (ASR) rules and hardening policies (e.g. “block JavaScript or VBScript from launching downloaded executables”) can break standard chains and reduce blast radius (Microsoft security guidance). Pair AV with EDR for the most effective results. In the PyPI examples, encryption (e.g. Fernet) and deferred decryption were used to evade static signatures (Checkmarx).
Browser Isolation and Hardening
Remote Browser Isolation (RBI) executes untrusted web code in a remote container and streams a safe rendering to the user. This neutralises drive-by chains by design; malware detonates in the container, not on the endpoint. Solutions can sanitise downloads server-side before delivery. Combine with SmartScreen/Safe Browsing and browser hardening for strong protection (Cloudflare RBI, Cloudflare Zero Trust).
User Training and Awareness
Security awareness that includes malvertising, SEO poisoning, and supply-chain risks helps users and developers spot anomalies (sponsored results, typosquatted domains, suspicious redirects). Simulated exercises improve vigilance. Training is not sufficient on its own, as modern lures are highly convincing; however, it reduces the likelihood of incidents and amplifies technical controls (e.g., users heeding SmartScreen warnings) (BleepingComputer).
Historical Perspective and Evolution
Today’s techniques build on a decade of SEO-driven and malvertising threats. The 2021 SolarMarker campaign revived SEO poisoning with keyword-stuffed PDFs on compromised WordPress sites and oversized installers tuned to evade content filters and sandboxes—patterns now common in AI-themed lures (Menlo Security). Supply-chain abuse has likewise evolved from isolated incidents to automated, at-scale operations across ecosystems (PyPI, npm), characterised by dependency confusion, repository hijacking, and fake mirrors. Abuse of cloud services for C2 (once the domain of APTs) has been democratised to commodity crimeware (see The Hacker News).
Defenders have responded with defence-in-depth: sandboxing in the 2010s, EDR over the last 5–6 years, and more recently, zero trust and isolation models. Each uplift forces the attacker to adapt. This is another reason to avoid relying on any single control.
Conclusion
Trusted channels have become unwitting conduits for malware. From GitHub repos teeming with trojans, to sponsored results delivering infostealers, to malicious packages in official repositories, adversaries are subverting the trust we place in common platforms. The infostealers delivered through these channels are modular, stealthy, and fast, posing a challenge to traditional detection methods.
To counter this, organisations should implement a defence in depth that combines:
- Preventative layers: reputation filtering, application allow-listing, RBI, and hardening.
- Detective/reactive layers: sandbox detonation, EDR/XDR in block mode, rapid credential/session revocation, and host isolation.
- Operational enablers include regular patching, aggressive takedowns, and threat intelligence sharing across the community.
No single control is foolproof; attackers explicitly design to evade one layer at a time. Multiple, independent safeguards, plus informed users and developers, raise the cost for attackers and disrupt the kill chain from end to end.
Sources and Further Reading
- Menlo Security – SolarMarker/SEO Poisoning
- Microsoft Security Blog
- BleepingComputer – Malware & Security News
- Zscaler ThreatLabz Research
- Hunt.io – Threat Research
- The Hacker News – Malware Coverage
- Checkmarx – Supply-Chain Research
- Datadog Security Labs
- Cloudflare – Browser Isolation